本サイトは、快適にご利用いただくためにクッキー(Cookie)を使用しております。
Cookieの使用に同意いただける場合は「同意する」ボタンを押してください。
なお本サイトのCookie使用については、「個人情報保護方針」をご覧ください。
Over the past year, we made an extensive research on the (in)security of embedded devices, such as routers, cameras, and toys. As a result, we identified a bunch of serious vulnerabilities. Interestingly enough, some of these devices were based on non-Linux systems, whereas most of them were embedded Linux systems.
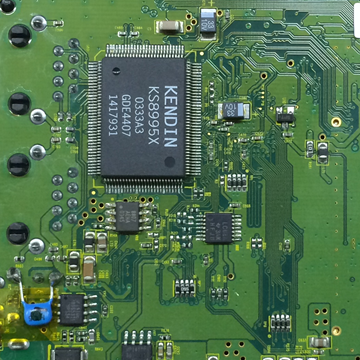
We take a classic Aterm WL5400AP router from NEC as an example. The manufacturer ended its production in 2007, but fortunately you can still download the latest firmware from their support website. The device runs VxWorks. It’s "the industry’s leading real-time operating system"[1]. Yeah, it's a Real-Time Operating System (RTOS)!
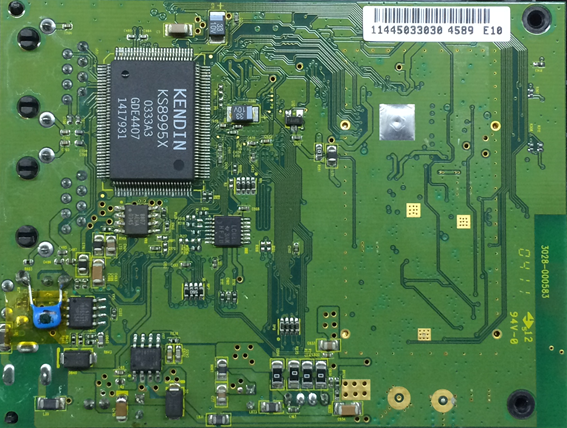
Fig.1 Aterm WL5400AP
VxWorks is a somewhat freaky operating system. It's totally different from modern general purpose operating systems like Linux. The lack of a memory protection mechanism and separation between kernel space and user space are just some examples. These are differences in design. VxWorks is used exclusively for embedded devices as opposed to workstations or servers.
As our focus is also on non-Linux based devices like Programmable Logic Controllers (PLCs) and Electronic Control Units (ECUs), VxWorks is a target worth working on.
Aterm WL5400AP has a telnet interface that listens on TCP port 2323. You can log in to the interface using the admin's password that you chose when you first setup the device. If you hit the help command, tons of commands are shown.
>telnet 192.168.0.204 2323 AP login: admin Password: ********************************* Atheros Access Point Rev 4.1.2.56 wlan1 -> help List of Access Point CLI commands: add remoteWbr -- Add a remote Wireless Bridge config wlan -- config wlanX connect bss -- connect to bssX del acl -- Delete Access Control List del key -- Delete Encryption key ...(snip)... set wmm -- Set WMM Mode set wmmParamBss -- Set WMM parameters used by STAs in this BSS set wmmParam -- Set WMM parameters used by this AP timeofday -- Display Current Time of Day version -- Software version wlan1 ->
But if you want to make the most out of the telnet service, you need to grab the firmware and explore it to discover hidden commands. One of such commands is the root command, which corresponds to the function defined at 0x8015E370 for the latest firmware.
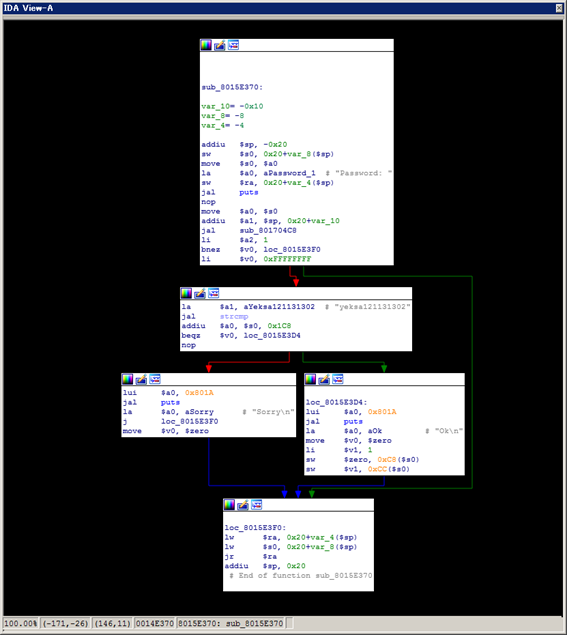
root is a command to escalate the privilege of admin. It requires a user input, which is compared with a hardcoded string "yeksa121131302". If they match, you'll get the privilege escalated and 100+ additional useful commands unlocked. You can see the list of new commands by hitting the help command again.
wlan1 -> root Password: ************** Ok wlan1 -> help List of Access Point CLI commands: ? -- Display CLI Command List add remoteWbr -- Add a remote Wireless Bridge root -- Temporary factory admin boot flash -- Boot from flash boot ethernet -- Boot from network ...(snip)... spy stop -- Stop spy start wlan -- Start the current wlan stop wlan -- Stop the current wlan timeofday -- Display Current Time of Day version -- Software version wlan1 ->
These commands are supposedly intended for developers, but such features are oftentimes abused by attackers. This time I unlocked the features just for fun!
References:
[1] VxWorks
https://www.windriver.com/products/vxworks/
[2] WL5400AP
おすすめ記事